Threats exposed, posture verified.
Assess cybersecurity maturity, vulnerability exposure, and incident readiness with the depth your deals demand, before hidden risks become post-close liabilities.
Book a demo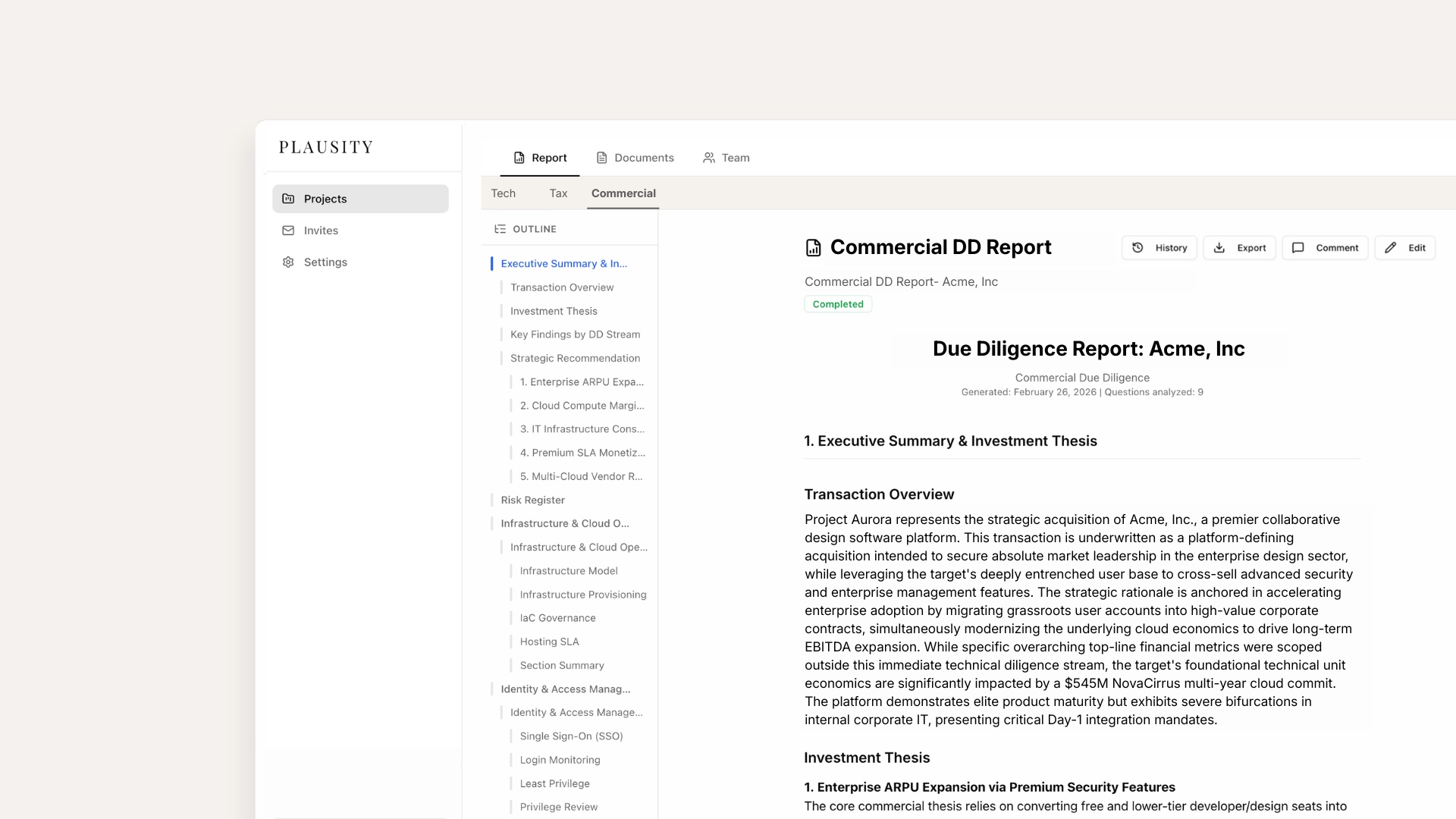
Know the security posture before you sign.
Assess vulnerability exposure and attack surface
Plausity analyses penetration test results, vulnerability scan reports, and infrastructure documentation to quantify the target's external attack surface. It flags unpatched systems, exposed services, and known CVEs, mapping each finding to potential business impact and remediation cost.
| Metric | Target | Benchmark | |
|---|---|---|---|
| Vulnerability Score | 68 | 45 | ↓ |
| Patch Compliance | 74% | 95% | ↓ |
| Infrastructure Resilience | 82% | 90% | ↓ |
Evaluate security operations and incident readiness
Review security operations documentation, incident response plans, SIEM configurations, and historical breach data. Plausity surfaces signals about security maturity (from mean time to detect to backup recovery testing) that indicate whether the target can withstand a real-world attack.
Verify compliance with security frameworks and standards
Automatically evaluate the target's compliance posture against SOC 2, ISO 27001, NIST CSF, CIS Controls, and GDPR technical requirements. Plausity identifies certification gaps, expired audits, and areas where stated compliance doesn't match operational evidence.
Produce cyber DD reports that drive decisions
Generate structured cybersecurity assessments covering vulnerability exposure, security controls, compliance posture, and incident readiness, with clear risk ratings and prioritised remediation recommendations that investors and operators can act on immediately.
Explore the Plausity platform
Plausity uncovered a critical unpatched vulnerability in the target's customer-facing infrastructure that had been missed in two prior audits. That single finding justified the entire cybersecurity DD workstream and reshaped our risk allocation.
Frequently asked questions
Plausity focuses on analysing security documentation, audit reports, and infrastructure configurations within the data room. For active testing, findings can be cross-referenced with outputs from your preferred penetration testing providers.
Plausity evaluates compliance against SOC 2 Type II, ISO 27001, NIST Cybersecurity Framework, CIS Controls, OWASP, and GDPR technical requirements. Custom frameworks and proprietary scoring methodologies can be configured per engagement.
Cybersecurity findings feed directly into the broader technology assessment. Infrastructure vulnerabilities inform architecture risk scores, and compliance gaps are cross-referenced with operational and regulatory diligence.
Yes. Plausity analyses cloud security documentation, IAM policies, network configurations, and compliance reports across AWS, Azure, GCP, and hybrid environments.
Cyber risk is deal risk. See it before you sign.
Book a demo and discover how Plausity helps you evaluate cybersecurity posture with rigour and speed.
Book a Demo